built from commit eabddf3d72
dated 2026-03-30 23:24:18 +0200
by Stéphane Lesimple (speed47_github@speed47.net)
18 KiB
Spectre & Meltdown Checker
A shell script to assess your system's resilience against the several transient execution CVEs that were published since early 2018, and give you guidance as to how to mitigate them.
| CVE | Aliases | Impact | Mitigation | Perf. impact |
|---|---|---|---|---|
| CVE-2017-5753 | Spectre V1 | Kernel & all software | Recompile with LFENCE-inserting compiler | Negligible |
| CVE-2017-5715 | Spectre V2 | Kernel | Microcode (IBRS) and/or retpoline | Medium to high |
| CVE-2017-5754 | Meltdown | Kernel | Kernel update (PTI/KPTI) | Low to medium |
| CVE-2018-3640 | Variant 3a | Kernel | Microcode update | Negligible |
| CVE-2018-3639 | Variant 4, SSB | JIT software | Microcode + kernel update | Low to medium |
| CVE-2018-3615 | Foreshadow (SGX) | SGX enclaves | Microcode update | Negligible |
| CVE-2018-3620 | Foreshadow-NG (OS/SMM) | Kernel & SMM | Kernel update (PTE inversion) | Negligible |
| CVE-2018-3646 | Foreshadow-NG (VMM) | VMM/hypervisors | Kernel update (L1d flush) or disable EPT/SMT | Low to significant |
| CVE-2018-12126 | MSBDS, Fallout | Kernel | Microcode + kernel update (MDS group) | Low to significant |
| CVE-2018-12130 | MFBDS, ZombieLoad | Kernel | Microcode + kernel update (MDS group) | Low to significant |
| CVE-2018-12127 | MLPDS, RIDL | Kernel | Microcode + kernel update (MDS group) | Low to significant |
| CVE-2019-11091 | MDSUM, RIDL | Kernel | Microcode + kernel update (MDS group) | Low to significant |
| CVE-2019-11135 | TAA, ZombieLoad V2 | Kernel | Microcode + kernel update | Low to significant |
| CVE-2018-12207 | iTLB Multihit, No eXcuses | VMM/hypervisors | Disable hugepages or update hypervisor | Low to significant |
| CVE-2020-0543 | SRBDS, CROSSTalk | All software (RDRAND/RDSEED) | Microcode + kernel update | Low |
| CVE-2022-40982 | Downfall, GDS | Kernel & all software | Microcode update or disable AVX | Negligible to significant (AVX-heavy) |
| CVE-2023-20569 | Inception, SRSO | Kernel & all software | Kernel + microcode update | Low to significant |
| CVE-2023-20593 | Zenbleed | Kernel & all software | Kernel (MSR bit) or microcode update | Negligible |
| CVE-2023-23583 | Reptar | All software | Microcode update | Low |
| CVE-2024-36350 | TSA-SQ | Kernel & all software (AMD) | Microcode + kernel update; SMT increases exposure | Low to medium |
| CVE-2024-36357 | TSA-L1 | Kernel & all software (AMD) | Microcode + kernel update | Low to medium |
Detailed CVE descriptions
CVE-2017-5753 — Bounds Check Bypass (Spectre Variant 1)
An attacker can train the branch predictor to mispredict a bounds check, causing the CPU to speculatively access out-of-bounds memory. This affects all software, including the kernel, because any conditional bounds check can potentially be exploited. Mitigation requires recompiling software and the kernel with a compiler that inserts LFENCE instructions (or equivalent speculation barriers like array_index_nospec) at the proper positions. The performance impact is negligible because the barriers only apply to specific, targeted code patterns.
CVE-2017-5715 — Branch Target Injection (Spectre Variant 2)
An attacker can poison the Branch Target Buffer (BTB) to redirect speculative execution of indirect branches in the kernel, leaking kernel memory. Two mitigation strategies exist: (1) microcode updates providing IBRS (Indirect Branch Restricted Speculation), which flushes branch predictor state on privilege transitions — this has a medium to high performance cost, especially on older hardware; or (2) retpoline, a compiler technique that replaces indirect branches with a construct the speculator cannot exploit — this has a lower performance cost but requires recompiling the kernel and sensitive software.
CVE-2017-5754 — Rogue Data Cache Load (Meltdown)
On affected Intel processors, a user process can speculatively read kernel memory despite lacking permission. The CPU eventually raises a fault, but the data leaves observable traces in the cache. Mitigation is entirely kernel-side: Page Table Isolation (PTI/KPTI) unmaps most kernel memory from user-space page tables, so there is nothing to speculatively read. The performance impact is low to medium, mainly from the increased TLB pressure caused by switching page tables on every kernel entry and exit.
CVE-2018-3640 — Rogue System Register Read (Variant 3a)
Similar to Meltdown but targeting system registers: an unprivileged process can speculatively read privileged system register values (such as Model-Specific Registers) and exfiltrate them via a side channel. Mitigation requires a microcode update only — no kernel changes are needed. Performance impact is negligible.
CVE-2018-3639 — Speculative Store Bypass (Variant 4)
The CPU may speculatively load a value from memory before a preceding store to the same address completes, reading stale data. This primarily affects software using JIT compilation (e.g. JavaScript engines, eBPF), where an attacker can craft code that exploits the store-to-load dependency. No known exploitation against the kernel itself has been demonstrated. Mitigation requires a microcode update (providing the SSBD mechanism) plus a kernel update that allows affected software to opt in to the protection via prctl(). The performance impact is low to medium, depending on how frequently the mitigation is activated.
CVE-2018-3615 — L1 Terminal Fault (Foreshadow, SGX)
The original Foreshadow attack targets Intel SGX enclaves. When a page table entry's Present bit is cleared, the CPU may still speculatively use the physical address in the entry to fetch data from the L1 cache, bypassing SGX protections. An attacker can extract secrets (attestation keys, sealed data) from SGX enclaves. Mitigation requires a microcode update that includes modifications to SGX behavior. Performance impact is negligible.
CVE-2018-3620 — L1 Terminal Fault (Foreshadow-NG, OS/SMM)
A generalization of Foreshadow beyond SGX: unprivileged user-space code can exploit the same L1TF mechanism to read kernel memory or System Management Mode (SMM) memory. Mitigation requires a kernel update that implements PTE inversion — marking non-present page table entries with invalid physical addresses so the L1 cache cannot contain useful data at those addresses. Performance impact is negligible because PTE inversion is a one-time change to the page table management logic with no runtime overhead.
CVE-2018-3646 — L1 Terminal Fault (Foreshadow-NG, VMM)
A guest VM can exploit L1TF to read memory belonging to the host or other guests, because the hypervisor's page tables may have non-present entries pointing to valid host physical addresses still resident in L1. Mitigation options include: flushing the L1 data cache on every VM entry (via a kernel update providing L1d flush support), disabling Extended Page Tables (EPT), or disabling Hyper-Threading (SMT) to prevent a sibling thread from refilling the L1 cache during speculation. The performance impact ranges from low to significant depending on the chosen mitigation, with L1d flushing on VM entry being the most practical but still measurable on VM-heavy workloads.
CVE-2018-12126 — Microarchitectural Store Buffer Data Sampling (MSBDS, Fallout)
CVE-2018-12130 — Microarchitectural Fill Buffer Data Sampling (MFBDS, ZombieLoad)
CVE-2018-12127 — Microarchitectural Load Port Data Sampling (MLPDS, RIDL)
CVE-2019-11091 — Microarchitectural Data Sampling Uncacheable Memory (MDSUM, RIDL)
These four CVEs are collectively known as "MDS" (Microarchitectural Data Sampling) vulnerabilities. They exploit different CPU internal buffers — store buffer, fill buffer, load ports, and uncacheable memory paths — that can leak recently accessed data across privilege boundaries during speculative execution. An unprivileged attacker can observe data recently processed by the kernel or other processes. Mitigation requires a microcode update (providing the MD_CLEAR mechanism) plus a kernel update that uses VERW to clear affected buffers on privilege transitions. Disabling Hyper-Threading (SMT) provides additional protection because sibling threads share these buffers. The performance impact is low to significant, depending on the frequency of kernel transitions and whether SMT is disabled.
CVE-2019-11135 — TSX Asynchronous Abort (TAA, ZombieLoad V2)
On CPUs with Intel TSX, a transactional abort can leave data from the line fill buffers in a state observable through side channels, similar to the MDS vulnerabilities but triggered through TSX. Mitigation requires a microcode update plus kernel support to either clear affected buffers or disable TSX entirely (via the TSX_CTRL MSR). The performance impact is low to significant, similar to MDS, with the option to eliminate the attack surface entirely by disabling TSX at the cost of losing transactional memory support.
CVE-2018-12207 — Machine Check Exception on Page Size Changes (iTLB Multihit, No eXcuses)
A malicious guest VM can trigger a machine check exception (MCE) — crashing the entire host — by creating specific conditions in the instruction TLB involving page size changes. This is a denial-of-service vulnerability affecting hypervisors running untrusted guests. Mitigation requires either disabling hugepage use in the hypervisor or updating the hypervisor to avoid the problematic iTLB configurations. The performance impact ranges from low to significant depending on the approach: disabling hugepages can substantially impact memory-intensive workloads.
CVE-2020-0543 — Special Register Buffer Data Sampling (SRBDS, CROSSTalk)
Certain special CPU instructions (RDRAND, RDSEED, EGETKEY) read data through a shared staging buffer that is accessible across all cores via speculative execution. An attacker running code on any core can observe the output of these instructions from a victim on a different core, including extracting cryptographic keys from SGX enclaves (a complete ECDSA key was demonstrated). This is notable as one of the first cross-core speculative execution attacks. Mitigation requires a microcode update that serializes access to the staging buffer, plus a kernel update to manage the mitigation. Performance impact is low, mainly affecting workloads that heavily use RDRAND/RDSEED.
CVE-2022-40982 — Gather Data Sampling (GDS, Downfall)
The AVX GATHER instructions can leak data from previously used vector registers across privilege boundaries through the shared gather data buffer. This affects any software using AVX2 or AVX-512 on vulnerable Intel processors. Mitigation is provided by a microcode update that clears the gather buffer, or alternatively by disabling the AVX feature entirely. Performance impact is negligible for most workloads but can be significant (up to 50%) for AVX-heavy applications such as HPC and AI inference.
CVE-2023-20569 — Return Address Security (Inception, SRSO)
On AMD Zen 1 through Zen 4 processors, an attacker can manipulate the return address predictor to redirect speculative execution on return instructions, leaking kernel memory. Mitigation requires both a kernel update (providing SRSO safe-return sequences or IBPB-on-entry) and a microcode update (providing SBPB on Zen 3/4, or IBPB support on Zen 1/2 — which additionally requires SMT to be disabled). Performance impact ranges from low to significant depending on the chosen mitigation and CPU generation.
CVE-2023-20593 — Cross-Process Information Leak (Zenbleed)
A bug in AMD Zen 2 processors causes the VZEROUPPER instruction to incorrectly zero register files during speculative execution, leaving stale data from other processes observable in vector registers. This can leak data across any privilege boundary, including from the kernel and other processes, at rates up to 30 KB/s per core. Mitigation is available either through a microcode update that fixes the bug, or through a kernel workaround that sets the FP_BACKUP_FIX bit (bit 9) in the DE_CFG MSR, disabling the faulty optimization. Either approach alone is sufficient. Performance impact is negligible.
CVE-2023-23583 — Redundant Prefix Issue (Reptar)
A bug in Intel processors causes unexpected behavior when executing instructions with specific redundant REX prefixes. Depending on the circumstances, this can result in a system crash (MCE), unpredictable behavior, or potentially privilege escalation. Any software running on an affected CPU can trigger the bug. Mitigation requires a microcode update. Performance impact is low.
CVE-2024-36350 — Transient Scheduler Attack, Store Queue (TSA-SQ)
On AMD Zen 3 and Zen 4 processors, the CPU's transient scheduler may speculatively retrieve stale data from the store queue during certain timing windows, allowing an attacker to infer data from previous store operations across privilege boundaries. The attack can also leak data between SMT sibling threads. Mitigation requires both a microcode update (exposing the VERW_CLEAR capability) and a kernel update (CONFIG_MITIGATION_TSA, Linux 6.16+) that uses the VERW instruction to clear CPU buffers on user/kernel transitions and before VMRUN. The kernel also clears buffers on idle when SMT is active. Performance impact is low to medium.
CVE-2024-36357 — Transient Scheduler Attack, L1 (TSA-L1)
On AMD Zen 3 and Zen 4 processors, the CPU's transient scheduler may speculatively retrieve stale data from the L1 data cache during certain timing windows, allowing an attacker to infer data in the L1D cache across privilege boundaries. Mitigation requires the same microcode and kernel updates as TSA-SQ: a microcode update exposing VERW_CLEAR and a kernel update (CONFIG_MITIGATION_TSA, Linux 6.16+) that clears CPU buffers via VERW on privilege transitions. Performance impact is low to medium.
Supported operating systems:
- Linux (all versions, flavors and distros)
- FreeBSD, NetBSD, DragonFlyBSD and derivatives (others BSDs are not supported)
For Linux systems, the tool will detect mitigations, including backported non-vanilla patches, regardless of the advertised kernel version number and the distribution (such as Debian, Ubuntu, CentOS, RHEL, Fedora, openSUSE, Arch, ...), it also works if you've compiled your own kernel. More information here.
Other operating systems such as MacOS, Windows, ESXi, etc. will most likely never be supported.
Supported architectures:
x86(32 bits)amd64/x86_64(64 bits)ARMandARM64- other architectures will work, but mitigations (if they exist) might not always be detected
Frequently Asked Questions (FAQ)
- What is the purpose of this tool?
- Why was it written?
- How can it be useful to me?
- How does it work?
- What can I expect from it?
All these questions (and more) have detailed answers in the FAQ, please have a look!
Easy way to run the script
- Get the latest version of the script using
curlorwget
curl -L https://meltdown.ovh -o spectre-meltdown-checker.sh
wget https://meltdown.ovh -O spectre-meltdown-checker.sh
- Inspect the script. You never blindly run scripts you downloaded from the Internet, do you?
vim spectre-meltdown-checker.sh
- When you're ready, run the script as root
chmod +x spectre-meltdown-checker.sh
sudo ./spectre-meltdown-checker.sh
Run the script in a docker container
With docker-compose
docker compose build
docker compose run --rm spectre-meltdown-checker
Note that on older versions of docker, docker-compose is a separate command, so you might
need to replace the two docker compose occurences above by docker-compose.
Without docker-compose
docker build -t spectre-meltdown-checker .
docker run --rm --privileged -v /boot:/boot:ro -v /dev/cpu:/dev/cpu:ro -v /lib/modules:/lib/modules:ro spectre-meltdown-checker
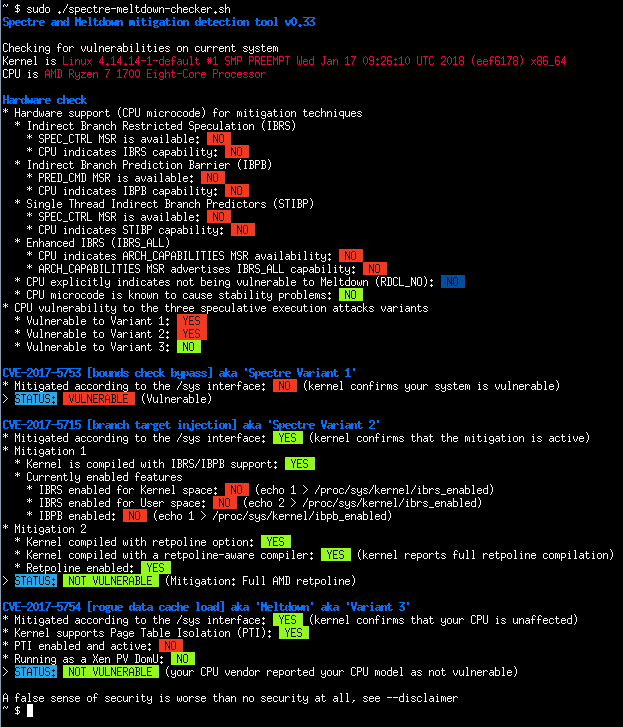
Example of script output
- Intel Haswell CPU running under Ubuntu 16.04 LTS
- AMD Ryzen running under OpenSUSE Tumbleweed
- Batch mode (JSON flavor)